Enterprise-grade security and compliance
Keeping your data safe is our main job. Unlike other tools that charge extra for security, Domo builds safety into every part of the platform from day one.
.avif)
Data protection for enterprises that scales
Domo meets security, compliance, and privacy requirements for regulated industries including financial services, healthcare, life sciences, government, and energy.
Organizational commitment
Domo's Security Council, made up of senior technology and business leaders, sets security policy, reviews risks, and ensures accountability across the company.
Built-in security features
Domo builds security, compliance, and privacy controls into the platform at the infrastructure, application, and data levels. Customers can also manage their own security settings directly.
Ongoing review
Domo reviews its security standards regularly against frameworks such as SOC 2, ISO 27001, and HIPAA.
Safety checked by experts
Domo completes third-party audits, compliance assessments, and annual penetration tests to meet customer and regulatory requirements. Current certifications include SOC 1, SOC 2, ISO 27001, ISO 27018, HIPAA, HITRUST, GDPR, and CCPA.

32%



Over 32% of Fortune 50 Global companies, including many of the largest organizations in the US, Europe, Asia, and Australia, trust Domo for robust, scalable data protection.
Security in every layer
High standards are built into the very foundation of how we store and move your data every day.
Domo's security framework includes:
- Multiple logical and physical security layers
- “Least privilege” and “separation of duties” access model
- Threat assessments of each new feature
- Transport layer encryption and encryption at rest
- Extensive logging and monitoring of network, system, and application events

32%



“We wanted to manage data as a corporate asset, and Domo was a good listener. They helped us draw a framework, an architecture, and a governance model that helped us achieve that.”
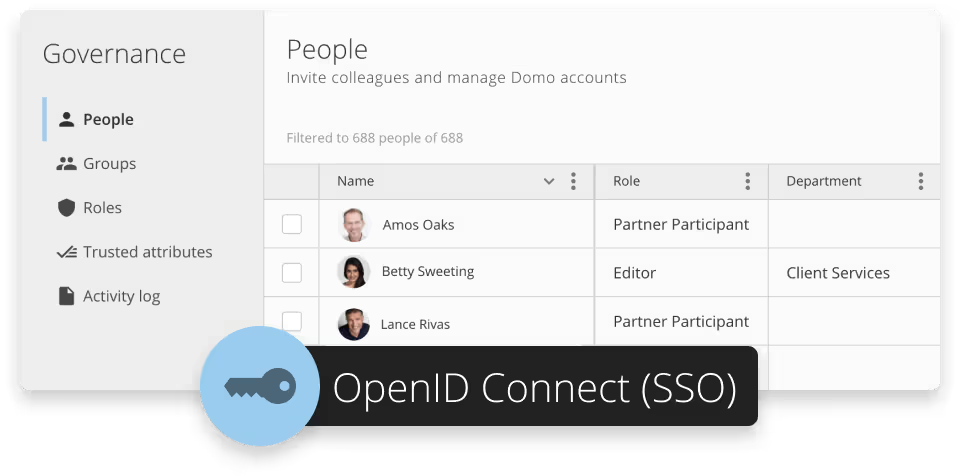
See the storyTools that put you in control
In addition to advanced internal security controls, Domo also gives customers direct control over their own security settings. These include single sign-on, multi-factor authentication, IP restrictions, and role-based access controls.
32%



"As the security officer, I was incredibly aware of the fact that we were putting sensitive information out there. We needed it to be permission-based so that not just anybody who logs into the gateway at a certain company could have access to all this information… Since everything was in the gateway already, we had the ability to make those logins very specific as to what you had access to, which we took advantage of."
See the storyBYOK encryption
With Bring Your Own Key (BYOK) encryption, you supply and control the encryption keys for your Domo environment. This lets you meet internal security policies without relying on Domo-managed keys. You can rotate encryption keys multiple times per day, on a schedule you define. If you revoke your encryption keys, all data in your Domo instance becomes immediately unreadable.

Responsible disclosure policy
While you manage your data, Domo's security team works with security researchers to review, reproduce, and respond to reported vulnerabilities.
Before disclosing any vulnerability publicly or to a third party, please report it privately to Domo first.
If you responsibly submit a vulnerability report to Domo, the Domo security team will:
- Promptly acknowledge receipt of your report
- Provide an estimated time frame for addressing the reported vulnerability
- Notify you when the vulnerability has been resolved

Stay in control of your data
Make sure the right people see the right info. You can set simple rules to keep your data safe as your team grows.
Explore Domo’s governance and security features.
Make data accessible while maintaining complete security and control.